Covering the world of cloud for more than a decade now, I’ve learned a simple thing: innovation should not and will not be focused too closely on security from the get-go. However, security cannot and should not be ignored as the cloud market matures and this is what we see here with the introduction of the 1st cloud security conference, AWS re:Inforce, taking place in Boston, June 25-26.
Back in the days when the market was still resistant to the public cloud, the discussion often centered around security of the environment and compliance. Public cloud opponents claimed that large enterprise and government organizations would not use the public cloud due to the risk of running sensitive workloads on a public facility. Now that the public cloud is a common go-to even for organizations with sensitive workloads, and AWS is the new IBM, this is no longer the case.
The Cloud Is Secured!
Examining the cloud trio of AWS, Azure, and Google, you will see that part of their agenda is to make the public cloud highly secure by default. In May, AWS published on their channels dozens of articles discussing security best practices and announcing new features. This included a white paper on how to architect for PCI DSS in order to separate workloads and secure sensitive ones. These vendors continually present new cloud security controls and tools to customers, as well as take responsibility for the risks and encourage their end consumers to do the same.
And this is where the inaugural AWS re:inforce event comes into the picture, both to serve an educational purpose, as well as to promote their major focus on securing their cloud. A major breach to their public cloud facilities can be devastating to their business and ecosystem. Further, as the cloud security vendor list grows it makes sense to give them their own platform for exposing their solutions to AWS users.
Moving to the Cloud Security Discussion
If you attended the last AWS re:Invent in Las Vegas as I did, you were one of 50,000 attendees, and you were probably overwhelmed by the schedule and event options. Keynotes, hundreds of education tracks, and hundreds of sponsors on the show floor parties force event-goers to pick and choose where they will focus their attention and what they will ignore. Realizing that security is only a small portion of the reInvent show, re:Inforce has a major role in the future of cloud computing and I am not talking about traditional cyber security aspects.
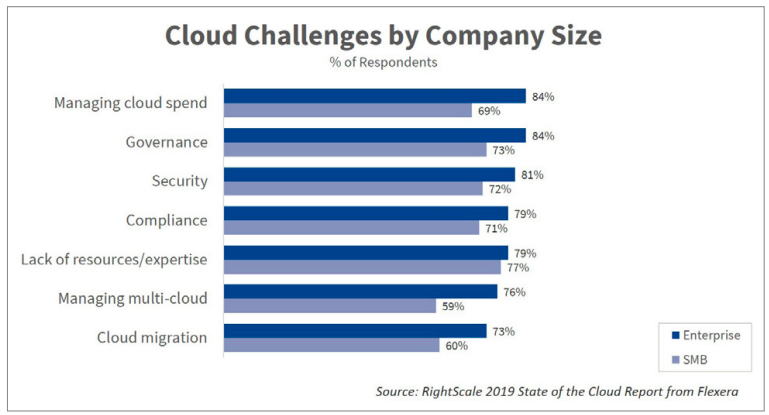
Discussing cloud security is different from the general conversation around cybersecurity. The elastic cloud environment generates additional challenges on top of the traditional cybersecurity ones. So we should expect that re:Inforce will deal with the typical cyber-related topics such as DDoS, Pentest, and Identity and Access. However, we also should expect coverage of cloud security aspects including secure migration, DevSecOps, and automated security control, encryption at scale, and data compliance; all using AWS-native controls.
Enterprise-grade Ecosystem to Complement Cloud-Native Controls
Cloud IT infrastructure revenues surpassed traditional IT infrastructure revenues for the first time in the third quarter of 2018, according to the IDC. The giant cloud is on the path toward conquering traditional IT (where the big money still is.)
While enhancing the security of their physical facilities, AWS also keeps introducing comprehensive tools such as AWS Security Hub, announced at AWS re:Invent last year. The hub gives you a comprehensive view of your high-priority security alerts and compliance status across AWS accounts. This is a purely traditional enterprise play, providing an all-in-one solution and support across a large enterprise environment (i.e. support of multiple AWS accounts). It clearly shows that AWS understands both the limitations, but also the priorities of their enterprise users and instead of expecting their customers to build their own “hub” based on AWS security building blocks, AWS, in a brilliant move, built it for them.
I already covered and discussed how the AWS ecosystem plays a key role in enabling the enterprise to run on the public infrastructure and when dealing with security, this is even more important. In such a rapidly growing enterprise cloud adoption, security solutions need to be delivered quickly, and keep a steady pace of new releases. AWS is aware of this and supports the growth of their ecosystem; specifically, the traditional security and compliance vendors. (For example, McAfee who has supported the enterprise market for more than three decades now.)
On the show floor of AWS re:Inforce you will be able to see other traditional vendors such Check Point (who acquired Dome9 this year), F5, Symantec, and even IBM, alongside younger but still established players such as Trend Micro, Sumo Logic, Imperva, Sophos, and Splunk. And let’s not forget the notable startups including Twistlock (recently acquired by Palo Alto Networks), Alcide, and Cloud Passage.
IOD Will Be There…Will You?
There aren’t a lot of third-party posts about what to expect at re:inforce — probably since it’s a first for all the attendees– but this one via threatstack may help!
Unfortunately I won’t be making it to Boston myself this year, but my colleague Jen Maidenberg (IOD’s VP of Marketing) will be walking the floor at the Security Learning Hub, and I know she’s eager to meet you in real life if you’re there, too. Find her on Twitter and send her a DM. Prior to her work at IOD, Jen’s spent her entire career in both marketing and content creation, so she’s a great resource for you if you have a content challenge you’re seeking to solve or just want to brainstorm.